A Hardware Security Module (HSM) protects encryption keys and sensitive data. Many organizations use this device to secure important systems.
Today, companies store large amounts of digital information. For example, they store customer records and financial data. Therefore, strong protection is necessary.
At the same time, cyber attacks continue to increase. Because of this trend, companies look for better security solutions. One common solution is the use of an HSM device.
What Is Cryptography?
To understand HSM technology, it helps to know Cryptography.
Cryptography protects information through encryption. In simple terms, it converts readable data into coded data.
Because of this process, unauthorized users cannot read the information. However, authorized users can decrypt it using a key.
For this reason, many industries depend on encryption. For example, banks use it to secure online transactions. Hospitals also use it to protect patient data.
Benefits of Using an Hardware Security Module Device
Many companies use this device because it offers several benefits.
Secure Key Storage
First, the device stores encryption keys in secure hardware. External systems cannot easily access these keys.
In addition, many devices follow standards such as FIPS 140-2. Because of this certification, organizations gain stronger protection.
Data Tokenization
Another important feature is tokenization. This process replaces sensitive data with random codes.
As a result, the original data stays hidden. Therefore, the risk of data leaks becomes lower.
Protection for Different Data States
Digital information exists in several states. For example, data may be stored, processed, or transferred.
Security systems must protect each state. With an HSM device, companies can protect data at rest, data in use, and data in motion.
Easier Key Management
Managing encryption keys can be difficult. However, centralized tools simplify the process.
Modern platforms support multi-cloud environments. Therefore, organizations can manage security systems more efficiently.
Hardware Security Module Levels
Security certifications help verify cryptographic device reliability.
One widely recognized standard is FIPS 140-2. This certification evaluates the security level of cryptographic modules.
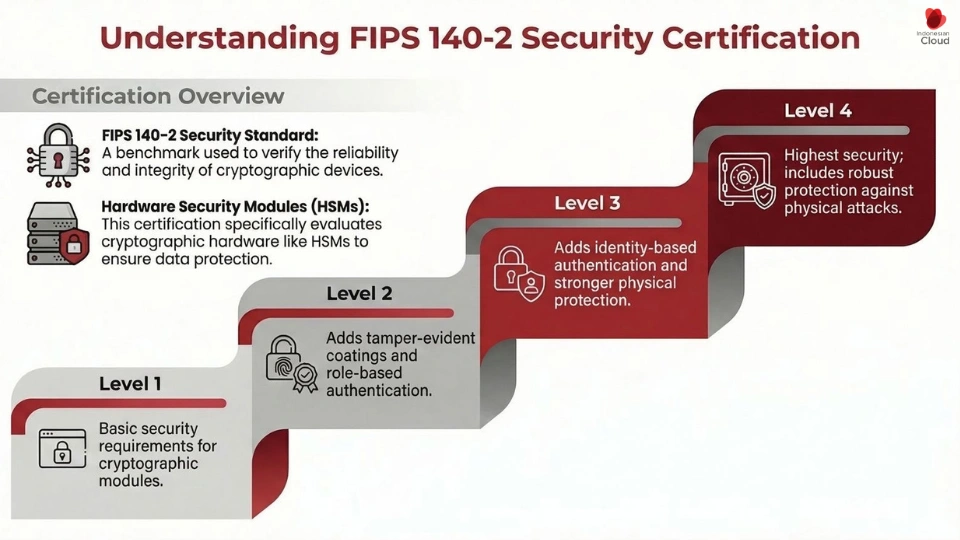
The framework defines four levels of protection.
Hardware Security Module Level 1 Security
Level 1 includes basic production-grade security requirements.
Hardware Security Module Level 2 Security
Level 2 introduces tamper-evident protection and role-based authentication.
Hardware Security Module Level 3 Security
Level 3 adds stronger physical protection and identity-based authentication.
Hardware Security Module Level 4 Security
Level 4 provides the highest level of protection against physical attacks.
Common Features in Hardware Security Module
Most HSM systems provide several important capabilities:
-
Encryption and key management
-
Data tokenization
-
Digital certificate protection
-
End-to-end encryption for applications
-
Public Key Infrastructure support
-
Virtual machine encryption
Because of these features, organizations can improve their cybersecurity systems.
Example Hardware Security Module in the Automotive Industry
Modern vehicles rely on digital systems. Many cars now connect to the internet.
For example, vehicle systems can communicate with other devices. However, this connectivity also creates security risks.
Therefore, manufacturers add security modules to vehicle systems.
Companies such as Microchip Technology develop chips that support secure boot and encryption. As a result, vehicles gain stronger protection against cyber attacks.
Conclusion
Data protection is essential for modern organizations. As digital systems grow, security risks also increase.
Therefore, companies need stronger security solutions. One effective technology is the Hardware Security Module.
With proper protection, organizations can keep their data secure and maintain customer trust.
If you are interested in learning more about Hardware Security Module services from Indonesian Cloud, please visit our website at indonesiancloud.com or our VPS website at cloudhostingaja.com. See you in our next article.

