Cloud computing security remains one of the most debated topics in modern IT. Many people still believe that cloud environments are less secure than traditional IT systems. However, this assumption often oversimplifies how security actually works.
People frequently ask a simple question: is cloud computing secure? The answer depends on how organizations design, implement, and manage security within the cloud.
One common concern involves accessibility. Many people believe cloud data becomes easier to access by unauthorized parties. Therefore, they assume attackers can exploit cloud systems more easily than on-premise infrastructure.
Understanding Cloud Computing Security
Before you decide whether cloud computing is secure, you need to understand how cloud security actually works. Cloud security follows the same core principles as traditional IT security.
In addition, organizations must apply security controls across multiple layers, including:
- Physical security for data centers
- Network protection
- Application security
- Data protection
- System security
- Governance and operational processes
Cloud environments also introduce an additional layer: virtualization security, which strengthens system isolation and resource control.
Key Challenges in Cloud Security
Cloud computing combines multiple infrastructure components into one ecosystem. As a result, organizations must actively manage security consistency across all layers.
In traditional IT environments, companies control the entire infrastructure directly. However, in cloud computing, providers and customers share responsibility. This shared model increases complexity and requires clear security boundaries.
Therefore, organizations must define responsibilities clearly to avoid security gaps.
Cloud Security Misconceptions
Many people assume external systems are less secure than internal ones. However, this belief does not always reflect reality.
Security in cloud computing depends on:
- How organizations manage resources
- Who controls access and governance
- How teams enforce policies and compliance
- How systems handle authentication and authorization
In addition, both cloud and on-premise environments can become secure or vulnerable depending on implementation quality.
What Determines Cloud Computing Security?
Cloud security risk depends on several key factors:
- Type of data and assets being managed
- Access control and governance models
- Security architecture implementation
- Compliance with standards and policies
- Application-level security protection
One of the most overlooked areas is application security. Many systems focus heavily on infrastructure protection but fail to secure applications properly.
Therefore, attackers often target applications because they are the easiest entry point into a system.
How Indonesian Cloud Ensures Security
Established in 2011, Indonesian Cloud is a trusted cloud service provider specializing in managed IT services based on on-demand, dynamic, and pay-per-use models.
Therefore, security is built into every layer of its cloud infrastructure.
Indonesian Cloud focuses on:
- Best-in-class certified technologies
- Top-tier infrastructure partners
- Skilled security professionals
- Secure data centers in Indonesia
CIA Security Model in Cloud Computing
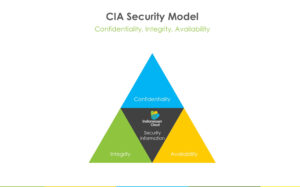
Indonesian Cloud applies the CIA Security Model (Confidentiality, Integrity, Availability) to ensure strong cloud security.
CIA Security Model
1. Confidentiality
Only authorized individuals, processes, or systems are granted access to information. All data is protected against unauthorized disclosure (e.g., hacking or cyberattacks).
2. Integrity
Information and systems are protected from unauthorized or accidental modification (e.g., hacking or attacks).
-
Data Integrity: Ensures information remains accurate, consistent, and trustworthy
-
System Integrity: Ensures systems function as intended
3. Availability
Systems and data are always accessible when needed. As a result, business continuity is maintained.
To support the CIA Security Model, Indonesian Cloud implements a comprehensive Security Architecture that ensures all aspects and processes align with CIA principles.

Additional Security Principles
To strengthen the CIA model, Indonesian Cloud also applies:
- Accountability
- Authentication
- Authorization
- Accounting
- Assurance
Furthermore, these principles ensure full traceability and control over all system activities.
Conclusion: Is Cloud Computing Secure?
Cloud computing is not inherently insecure. In fact, both cloud and traditional IT environments can be secure when properly designed and managed.
Therefore, cloud security depends on implementation, governance, and continuous monitoring—not on the deployment model itself.
At Indonesian Cloud, security is continuously strengthened through layered protection, certified infrastructure, and strict adherence to global security standards.
Closing Statement
Security is not static. There is no such thing as 100% security guarantee. However, organizations can significantly reduce risks by implementing strong security frameworks and trusted cloud providers.
This concludes our explanation. If you would like to read more technology-related articles or obtain further information about Indonesian Cloud products, please visit Indonesiancloud.com. See you in our next article.
Herwono W. Wijaya
Security & Virtualization Consultant @Indonesian Cloud